What we do
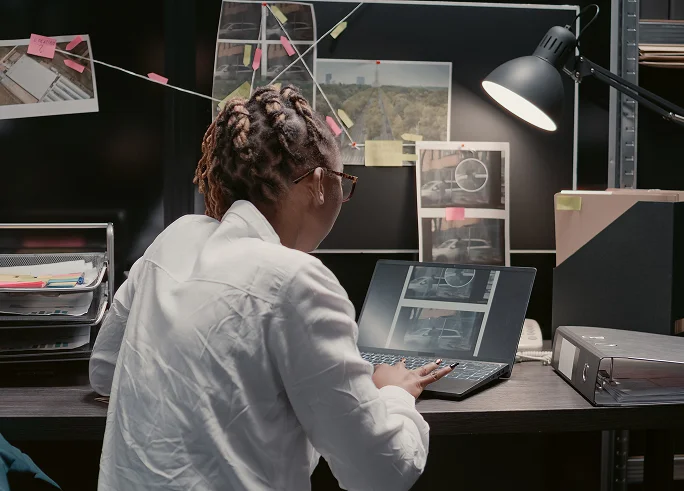
Data extraction
We extract information from a wide range of digital devices while meeting the highest legal standards.

Data extraction
We extract information from a wide range of digital devices while meeting the highest legal standards.
Technical Audit
We analyze collected information for evidentiary purposes or to validate hypotheses.

Technical Audit
We analyze collected information for evidentiary purposes or to validate hypotheses.
Detailed Documentation
We produce complete and certified copies of data retrieved from devices, while preserving the original evidence.

Detailed Documentation
We produce complete and certified copies of data retrieved from devices, while preserving the original evidence. These documents are then used for legal purposes such as demonstrating evidence, comparing versions, or conducting counter-analysis.
Applicable contexts

Professional Tools and Rigor
Our expertise is defined by the use of the most advanced forensic tools available, including Cellebrite UFED, Magnet AXIOM.
All our analyses follow strict protocols:
What you receive
A clear, detailed report from a certified computer forensics engineer.
A concise summary for the lawyer and/or judge.
Legally admissible evidence for use in court, negotiation, or mediation.
Peace of mind knowing that nothing has been overlooked.

Do you have a case?
Submit it through our secure platform.
Our experts are the only ones who will access your information, which is treated with full confidentiality.
Have Questions?
Contact Us
expertise@firmeh2e.com
Toll-free
1-888-796-8706
Phone/SMS
450-700-4233
